The hardware threat hiding in plain sight.
RSAC, the largest cybersecurity industry event, is wrapping up today. Hundreds of amazing compoanies presented their newest cyber-risk prevention technolog at the show. But here’s something almost nobody talks about: The hardware threat hiding in plain sight.
Every year, organizations pour billions of dollars into software security – firewalls, endpoint detection, encryption, network monitoring. And yet, a growing category of cyber threat operates beneath all of it, invisible to every tool in the standard security stack. It doesn’t exploit a vulnerability in your code. It doesn’t phish your employees. It arrives soldered onto a circuit board, hidden inside the very hardware your systems depend on.
Hardware-based cybersecurity threats are no longer theoretical. They are active, sophisticated, and increasingly difficult to detect using conventional means. For manufacturers and operators in defense, aerospace, data centers, and medical electronics, the question is no longer whether hardware security deserves attention – it’s whether your current approach is actually equipped to address it.
The Attack Surface Nobody Is Watching
Traditional cybersecurity assumes that the underlying hardware is trustworthy. That assumption is the gap that adversaries exploit. When a component is tampered with before it ever reaches your production line – reprogrammed with malicious firmware, substituted with a counterfeit part, or physically modified to introduce a covert communication channel – no amount of software-based monitoring will catch it. The threat is baked into the foundation.
The electronics supply chain creates abundant opportunities for exactly this kind of infiltration. Components are sourced from across the globe, passing through multiple tiers of distributors and manufacturers before reaching final assembly. State-sponsored actors and sophisticated criminal networks have demonstrated the ability to intercept and modify components within legitimate supply chains, long after they have left the original manufacturer’s facility. A microcontroller with unauthorized firmware. A re-marked chip that looks identical to the genuine article. A tiny component piggybacked onto a PCB, rerouting signals to a covert destination. These are not edge cases – they are documented, real-world attacks.
The challenge is compounded by the limits of conventional inspection. Sample-based X-ray analysis and manual visual checks cover only a fraction of components. They are too slow, too costly, and too incomplete for high-throughput production environments. More critically, they are not designed to detect the subtle physical signatures that distinguish a tampered component from a legitimate one.
Visual AI: Security at the Component Level
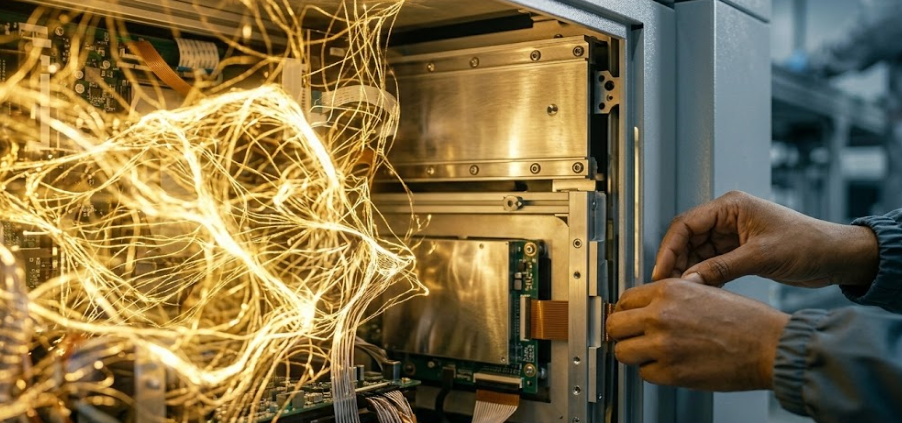
The answer to a hardware threat is a hardware solution – and that solution now exists at scale. Visual AI inspection, integrated directly into the SMT assembly process, brings systematic, real-time authentication to every single component.
During the pick-and-place process, high-resolution cameras already capture images of every component’s bottom side. By applying deep learning algorithms to this visual stream, it becomes possible to detect probe marks – the telltale signs of unauthorized programming or reprogramming – as well as subtle differences in package geometry, surface texture, and edge characteristics that indicate a counterfeit or substituted part. This level of scrutiny, applied to 100% of components, achieves anomaly detection accuracyexceeding 99.3%, compared to the incomplete and inconsistent results of traditional sampling approaches.
Post-assembly, top-side inspection of the completed board adds a second layer of defense. Deep learning models trained on expected board configurations can identify missing components, unauthorized additions, piggybacking – where a rogue component is stacked on top of a legitimate one – subtle marking inconsistencies, and even added wires introduced to modify circuit behavior or create hidden communication channels. These are physical modifications that would remain completely invisible to any traditional cybersecurity tool, and that could persist undetected within deployed systems for years.
Rethinking Where Security Begins
The cybersecurity conversation has matured enormously over the past decade. Organizations now understand that perimeter defense is not enough – that security must be layered, proactive, and embedded throughout the technology stack. The next evolution of that thinking extends the boundary all the way down to the component level, to the moment a chip is placed on a board.
Securing hardware at the point of manufacture is not just a quality assurance measure. It is a foundational cybersecurity requirement for any organization operating in a world where the supply chain itself has become an attack vector. Visual AI makes that requirement achievable – without adding new equipment, without slowing production, and without relying on the assumption that trust has been earned simply because a component arrived from a familiar source.
The firewall protects your network. Visual AI protects what the firewall cannot see.